The First Seadless Hardware Wallet
Losing a phone, switching devices, or hitting an incident shouldn’t mean starting over.
Sovrency delivers seedless simplicity with hardware-backed approvals
and recovery designed for the long run.

You
Shouldn't
have
to
choose
between
seedless
simplicity
and
hardware
security

Sovrency
is
built
to
deliver
both,
without
breaking
recovery.
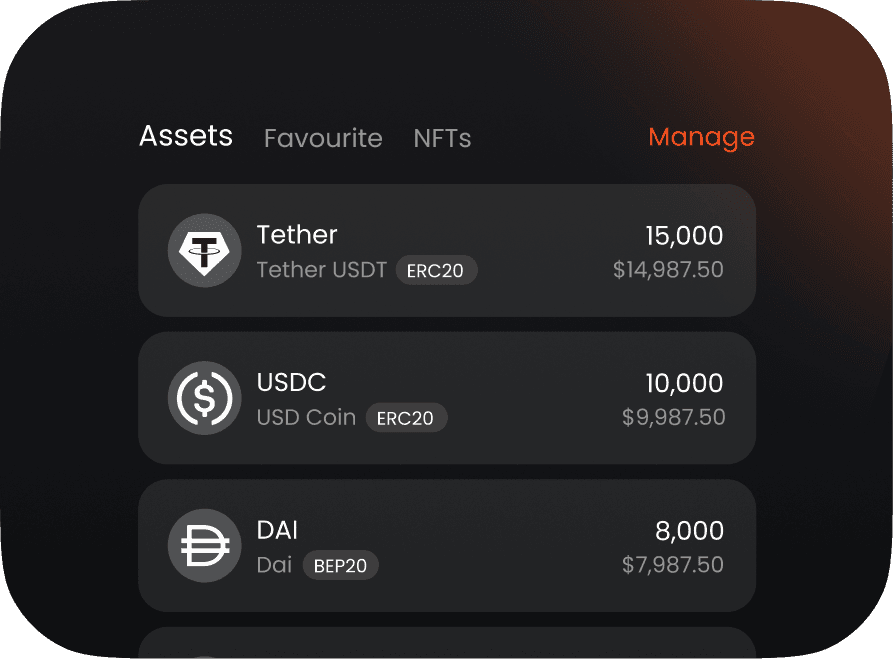
What you get

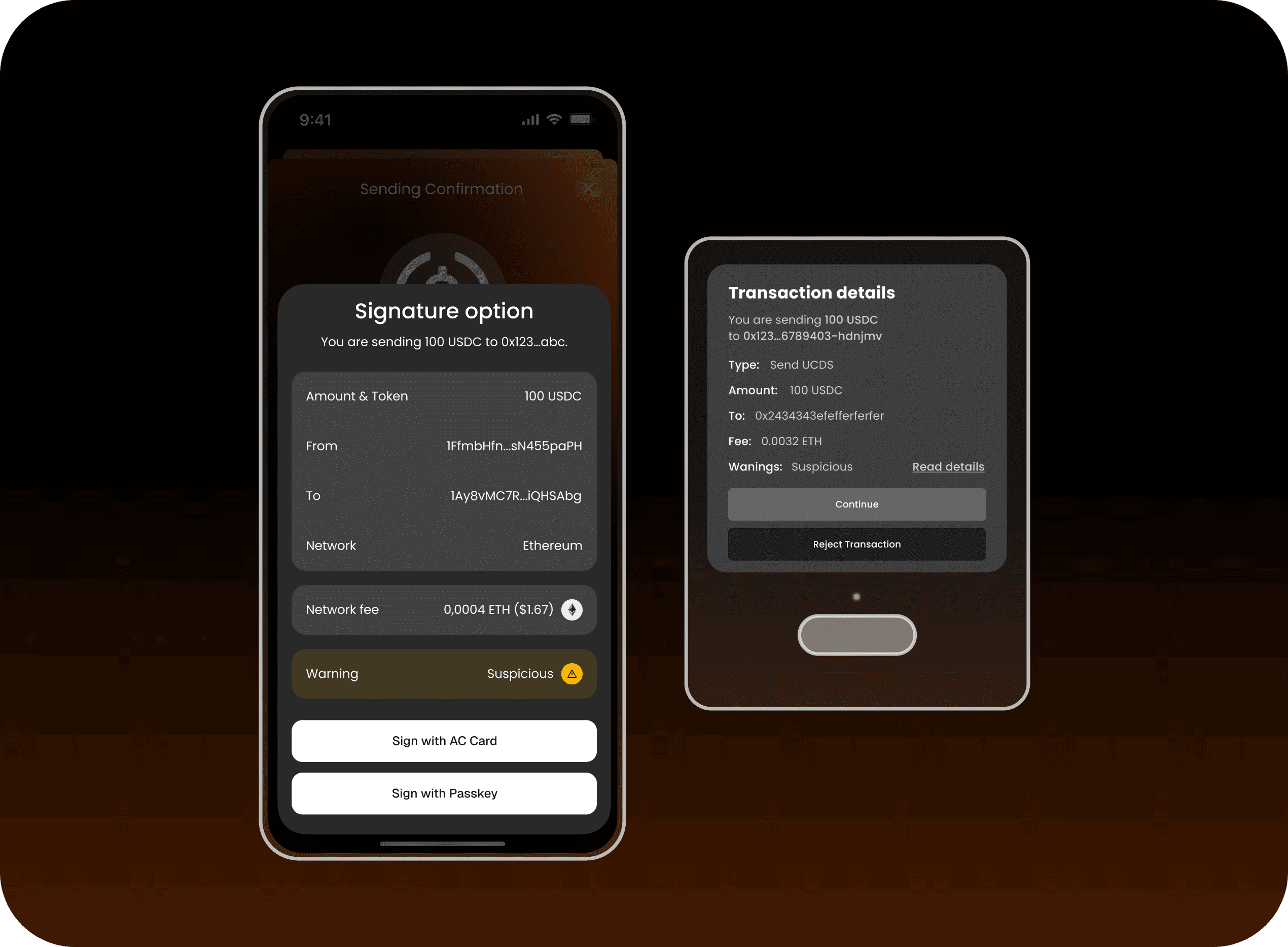
Everyday Transactions
Fast by default

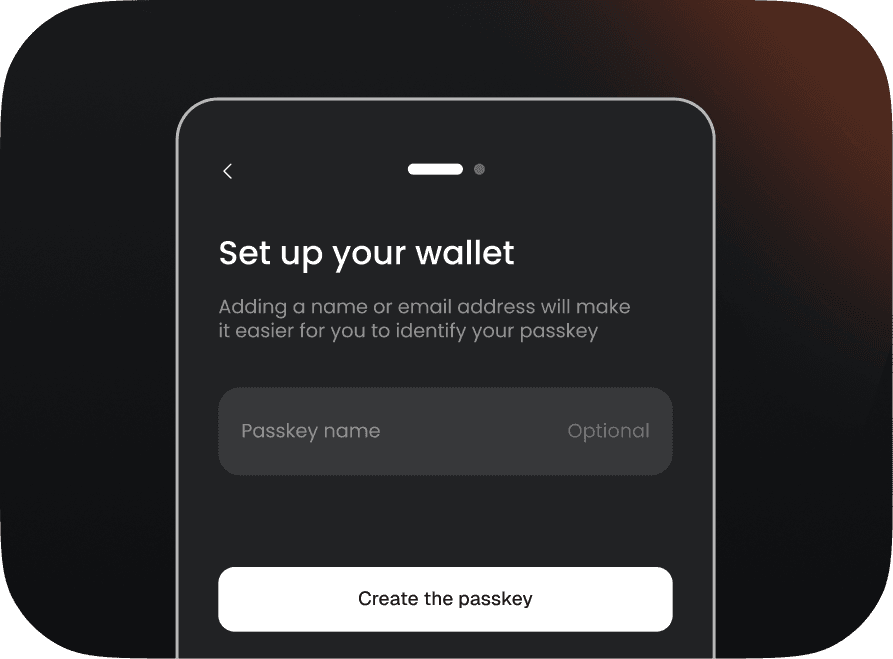
Passkey
First Security
Seedless Access
Under the Hood
Distributed keys,
Coordinated approvals
Sovrency replaces seed phrases with a distributed key system. Security comes from separation: a key share on your device, a hardened guardian share in the cloud, and an optional hardware share for independent confirmation. No single component is sufficient on its own.
Security Engine
Onboarding
From First Transaction to Sovereign Mode in 3 Steps
Our Stats
Blazing Fast
1 sec

Open Source
99%

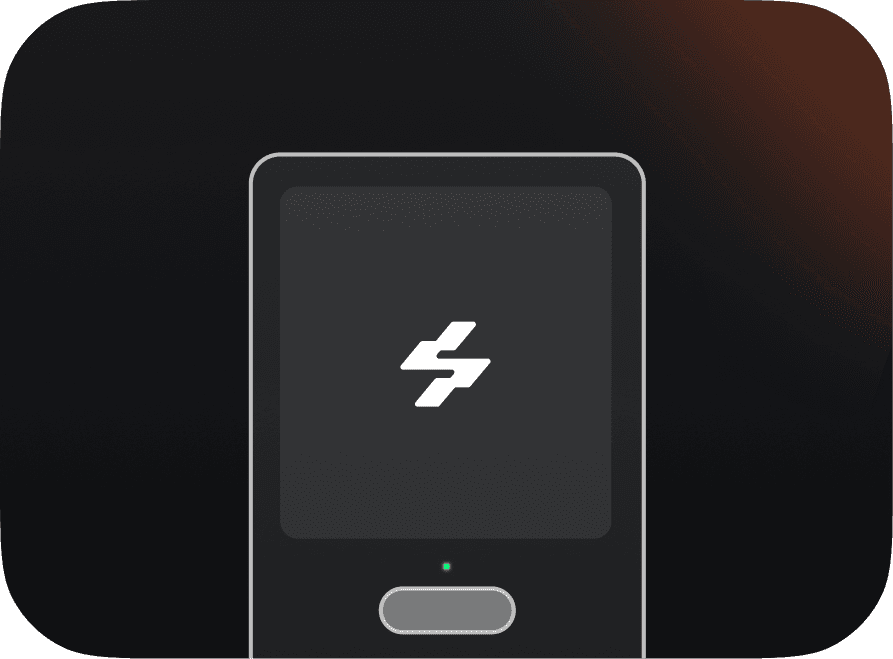
Silicon Key Security
EAL 6+

Lifecycle

Secure Foundation
Keys originate inside secure elements with zero exposure, forming a resilient base for long‑term protection.
Daily Use
Fast, reliable transactions secured by distributed keys, Transaction Policies, and SignSight verification.
Incidents
Loss phone or Silicon Key is resolved through secure rotation and Backup Card recovery without revealing secrets.
Continuity & Inheritance
Sovereign Mode adds hardware anchored durability for long‑term protection and secure continuity.
Questions Answered
FAQ’S
Everything you need to know about how Sovrency works, how we keep your assets safe, and what you can expect across Everyday and Sovereign Modes.
Blog
Learn with Sovrency

Self-Custody 2.0: Beyond Seed Phrases and Hardware
Upgrade from fragile seeds to durable, continuity-grade crypto self-custody today.

Designing Sovrency’s Silicon Key for Real Incidents
Hardware anchor designed for recovery when everything else fails badly.
Join Our Waitlist
Be the first to experience sovereign crypto security. Get early access, product updates, and exclusive insights straight to your inbox.